Enforce Password complexity is an important security measure that should be taken whenever possible. It is a way of ensuring that users have secure passwords and makes it more difficult for cyber attackers to guess the passwords of users.
That’s why in this tutorial we will see how to enforce password complexity on CentOS/RedHat.
To see how to enforce password complexity on Ubuntu/Debian click here.
CentOS/RedHat comes with a built-in feature for password complexity, which can be enabled to help protect user accounts from unauthorized access.
We can do that with 2 files either with system-auth located on /etc/pam.d or with pwquality.conf located on /etc/security.
To use pwquality.conf, the module pwquality must be installed, witch is by default.
Using system-auth file to enforce password complexity:
This file contains information about the authentication process, such as password complexity requirements.
We have to ensure that passwords meet certain criteria, such as containing upper and lowercase letters, numbers, and special characters
Below are the recommendations of the password we are going to use :
-at least 1 lower-case : lcredit=-1
-at least 1 upper-case : ucredit=-1
-at least 1 digit in the password : dcredit=-1
-at least 1 special characters : ocredit=-1
– Minimum length of a password : minlen=7
Edit system-auth file and locate the line containing the pam_pwquality.so module :
password requisite pam_pwquality.so try_first_pass local_users_only retry=3 authtok_type=

Comment the line and replace by the line below using the criteria recommended :
password requisite pam_pwquality.so try_first_pass local_users_only retry=3 authtok_type= minlen=7 lcredit=-1 ucredit=-1 dcredit=-1 ocredit=-1
If you want these configurations to also be applied for the root account, add the enforce_for_root option :
password requisite pam_pwquality.so try_first_pass local_users_only retry=3 authtok_type= minlen=7 lcredit=-1 ucredit=-1 dcredit=-1 ocredit=-1 enforce_for_root

Using pwquality.conf file :
Edit pwquality.conf file and locate the parameters that I mentioned earlier :
[root@linux ~]# grep -E 'minlen|lcredit|ucredit|ocredit|enforce_for_root' /etc/security/pwquality.conf # minlen = 8 # ucredit = 0 # lcredit = 0 # ocredit = 0 # enforce_for_root
As you can see all criteria as commented, uncomment them and set the correct configuration like we did earlier :
[root@linux ~]# grep -E 'minlen|lcredit|ucredit|ocredit|enforce_for_root' /etc/security/pwquality.conf minlen = 7 ucredit = -1 lcredit = -1 ocredit = -1 enforce_for_root
Testing Password Enforcement Policy :
As root I will create a user and give him a password that does not contain a number :

As you can see, the password has been refused since it does not contain a number.
Now I will try to give a password with a number but no capital letters :

As you can see the password was refused.
To read this article in French click here.



nmtui : Configurer une adresse IP sous Linux
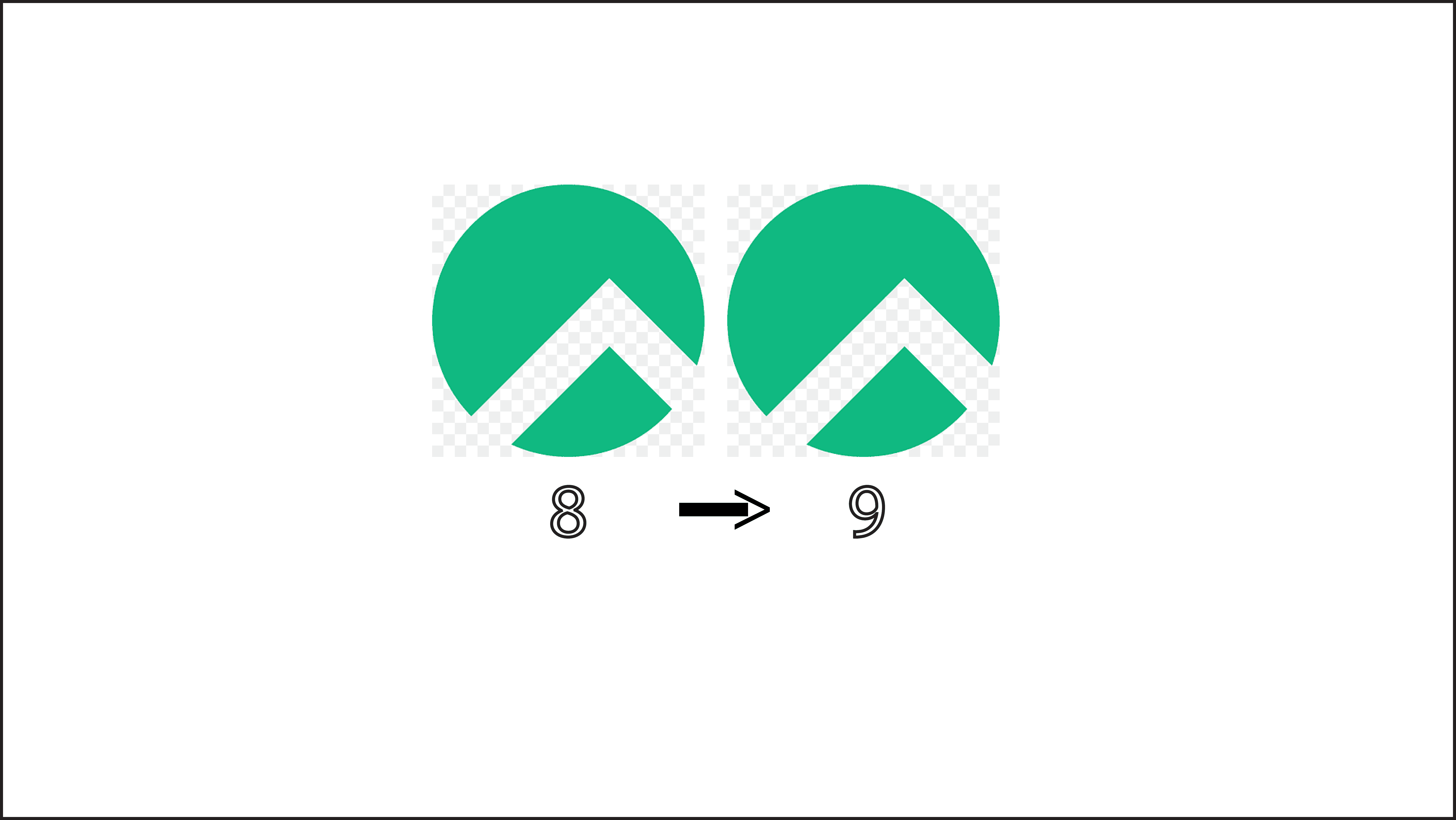
Migrer Rocky Linux 8 vers Rocky Linux 9
Définir temporairement une adresse IP sur un OS Linux
pkill : Comment arrêter les process avec leurs nom
Fail2Ban : How to protect Linux services