What is kubectl ?
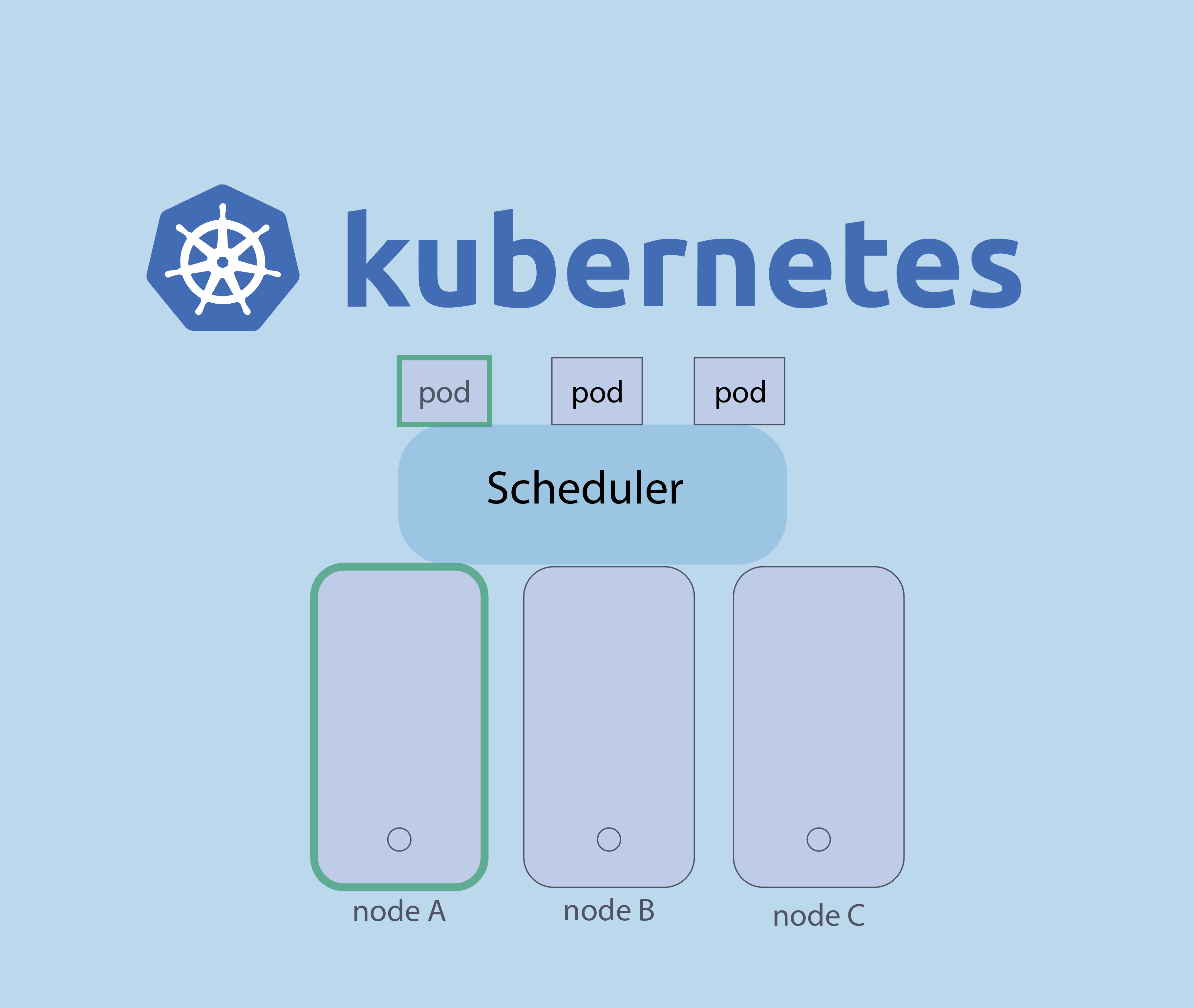
kubectl is the command-line interface (CLI) for Kubernetes, an open-source container orchestration system that automates the deployment, scaling, and management of containerized applications. kubectl allows you to run commands against Kubernetes clusters to deploy applications, inspect and manage cluster resources, and view logs.
With kubectl you can perform a variety of tasks, such as :
– Deploying applications to a cluster
– Scaling up or down the number of replicas of a deployment
– Updating the container image for a deployment
– Viewing the logs for a container
– Managing the rolling update of a deployment
– And much more!
In this article we will discuss about 15 kubectl command used on kubernetes.
15 most used command on kubernetes
– Retrieve information about one or more resources :
# kubectl get
–Show details of a specific resource or group of resources
# kubectl describe
– Create and update resources in a cluster
# kubectl apply
– Delete resources by filenames, stdin, resources and names, or by resources and label selector
# kubectl delete
– Create one or more resources from a file or from stdin
# kubectl create
– Edit a resource on the server
# kubectl edit
– Execute a command in a container
# kubectl exec
– Print the logs for a container in a pod
# kubectl logs
– Manage the rollout of a resource
# kubectl rollout
– Set a new size for a Deployment, ReplicaSet, or ReplicationController
# kubectl scale
– forward one or more local ports to a pod :
# kubectl port-forward
– Display Resource (CPU/Memory/Storage) usage :
# kubectl top
– Display addresses of the master and services
# kubectl cluster-info
– Display addresses of the master and services
# kubectl cluster-info
– View and modify kubeconfig files :
# kubectl config
– List all pods in the namespace :
# kubectl get pods
To learn more about kubectl you can visit the official documentation.





nmtui : Configurer une adresse IP sous Linux
Résoudre l’erreur : WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED!
Empêcher les utilisateurs sudoers d’exécuter des cmds sudo
Comment installer Nginx on Rocky Linux 9
Fail2Ban : How to protect Linux services